Customer data is vital for the growth and success of your business as it aids you in converting leads to customers and serving them better. Customer relationship management (CRM) solutions help you to store and manage such data. Over the past decade, Salesforce has become businesses’ go-to CRM solution. With the help of salesforce consultants, this cloud-based platform enables you to better manage your customer data, streamline processes, and boost sales.
As you entrust customers’ sensitive information to Salesforce, it’s critical to ensure robust security measures are in place to protect that data.
To help you bolster your security posture, we have compiled a list of 8 best security practices according to the top salesforce consultants in the industry.
8 Best Salesforce Security Practices According To Salesforce Consultants
With the constant threat of cyber-attacks and data breaches, robust security measures are paramount. Here are the 8 best ways recommended by top salesforce consultants to mitigate such risks:
1. Two-Factor Or Multifactor Authentication (MFA)
MFA or multifactor authentication is a secure authentication method that adds an extra layer of security to prevent unauthorized login. The user needs to prove their identity by providing additional proof apart from the password.
This extra proof can be verification codes sent to their mobile number, email or authenticator apps, login prompts on the mobile device, fingerprint scanning, facial recognition, security keys, etc.
MFA helps prevent unauthorized access to your Salesforce account even if someone manages to obtain your password. However, Salesforce consultants recommend sticking to only two-factor authentication (2FA), as more than 2 proofs can be cumbersome and annoying for your users.
2. Limited Access To IP Ranges
Salesforce works on a multi-tenant architecture where data and other resources are shared between the users with security and privacy. With Salesforce, you can restrict access using IP ranges to ensure only authorized users can access the platform. Users can log in to Salesforce only from designated IP addresses, usually from your organization’s network or VPN.
Additionally, you can enforce session reboots for inactivity and set up defined hours of usage for individual sessions. Once the session times out, the session will expire, and the user will be logged out. They will have to log in again to continue using the platform.
Also, employees often leave their computers open during meetings or lunch breaks, and there is the risk of an unauthorized person using their accounts. And session timeouts prevent this.
3. Secure Password Management
Salesforce consultants recommend setting up secure password management to protect your Salesforce data. Enforce strong password policies like a minimum password length of 8-10 characters and complexity – a combination of alphanumeric characters with lower and upper-case letters and symbols. You can also set up the passwords to expire (Salesforce recommends 90 days).
Afterward, the user will be directed to change the password when logging in. Implement password history to ensure the new password cannot match the previous 5 passwords. Limit the number of failed logins due to wrong passwords to a maximum of 3 or 5.
4. Profile Control Access And Permissions
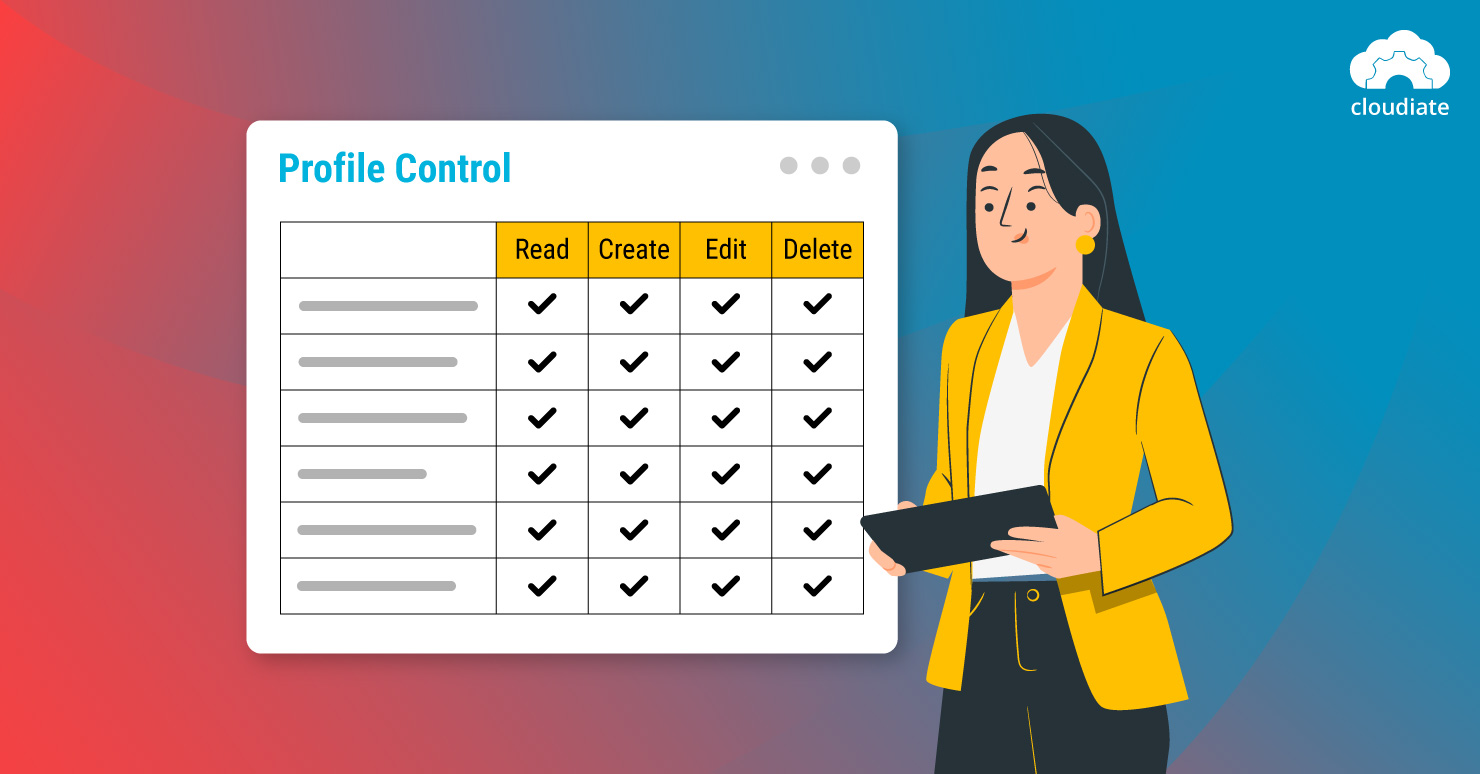
Controlling access to Salesforce data based on user roles and permissions can enhance security. Use profiles to define specific permissions for each user – what operations they can do and which data they can access. You can assign profiles to each user and set the permissions while creating their accounts. This way, they can access only the data they need to do their job.
However, bear in mind that profiles and permission sets can be flexible. You need to manage them properly else it will pose a huge risk to data security.
5. Regular New Encryption Key Generation
Salesforce provides encryption for the data stored on the platform and during data transfer to and from the platform. Encryption prevents data from getting exposed while exporting. If you are using platform encryption, regularly generate new encryption keys to maintain the integrity of your Salesforce data. Destroy the old encrypted keys right after decrypting the data.
To be safer, re-encrypt the encrypted data with new encryption keys irrespective of whether it is currently used, archived, or destroyed. This ensures any data stored or transmitted using encryption remains secure.
6. Regular Data Backup
Your system still risks data loss, corruption, and other threats, even with solid security measures. Regularly backing up your Salesforce data ensures you can recover the data in case of a disaster.
Have an effective backup and recovery system that automatically takes periodic backups (preferably daily), sends real-time incident alerts, can pinpoint impacted data, and seamlessly restores your system. This way, your most up-to-date data will be available for recovery in case of an emergency.
7. Periodic Health Checks And Audits
Periodic health checks and audits of your Salesforce instance can help you identify potential security risks and vulnerabilities. Use Salesforce’s Health Check tool, which grades basic security as low-risk, medium-risk, or high-risk in different categories. It also provides recommendations to address these security flaws.
Schedule periodic audits like reviewing user access logs, identifying inactive user accounts, and conducting penetration testing to identify potential security gaps. Audits identify irregular behaviors, procedure violations, usage trends, and unexpected changes.
8. Use Salesforce Shield
Salesforce consultants also recommend Salesforce Shield, a suite of security features that enhances the security of your Salesforce instance. It includes features such as enhanced encryption, data monitoring, data archiving, and security policy automation to help you meet compliance requirements and protect your data.
Salesforce Shield has four main features:
- Platform Encryption encrypts sensitive data using different encryption schemes for standard and custom fields.
-
- Event Monitoring tracks multiple event types to prevent, mitigate and monitor data threats.
- Field Audit Trail tracks data changes in various standard and custom objects and records the modifications.
- Data Detect finds and classifies critical, sensitive information like credit card details, social security numbers, etc.
Secure Your Business With Cloudiate
A CRM tool like Salesforce provides features and benefits that take your customer service and experience to a new level.
But deploying such a complex tool is not easy, and you need the help of expert salesforce consultants to manage installation, integration, and maintenance.
Cloudiate can handle all your security, technical, and business requirements and provides Salesforce training and support.
Contact us to get in touch with the best salesforce consultants today!

